Red Sun Windows LPE
TLDR
Microsoft defender lets you escalate privileges to local admin if you tag a file with the cloud attribute . The open source implementation focuses on TieringEngineService.exe and utilizes its COM methods to achieve code execution but you can also abuse the write primitive and execute the privileges. But TierinEngineService is not the only thing you can abuse
TOCTOU
Time-of-check to time-of-use (TOCTOU) is a race condition flaw where a program checks a resource’s state (e.g., file permissions) but that state changes before the program uses it. Attackers exploit this brief time gap to manipulate the resource, bypassing security checks. It is commonly used for symlink attacks and privilege escalation.
Red Sun RCE
Understanding the vulnerability and how it stems back to one of the most common windows vulnerabilities. The Red Sun exploits windows defender’s mechanism to classify and quarantine a malicious file . When you modify the attribute of a file with the ‘cloud’ tag , for some reason defender writes it back to its original location (the cloud tag is not a windows attribute but it is part of cloud files to classify a file as cloud-backed).So when you write a malicious file on-disk then windows defender,which is running with administrator privileges,accesses the file and upon noticing that is cloud-backed, it writes it back to the original location.
So if Malicious.txt is placed in C:\Users\Public\Temp defender will first quarantine the file. Subsequently, it will also place the Malicious.txt in the same location after it quarantines. The author of Red Sun used a simple EICAR file as his choice of malicious file. Couple that with the classic junction file trick and you have a write primitive on privileged directories.
The Red Sun utilizes TieringEngineService.exe and uses the COM
methods exposed to achieve code execution. 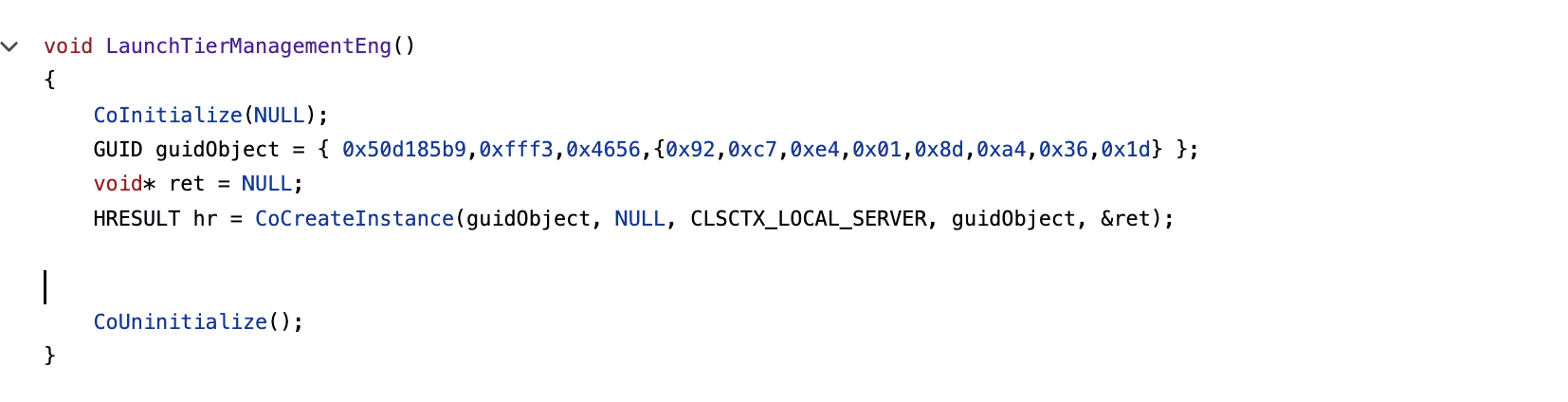
It is important to note that while this abuses the write primitive for privilege escalation Windows Defender must have created a vss shadow prior to this execution. This shadow is created only when windows defender has quarantined a file . So if the defender has never performed a quarantine, the exploit will just time out. In that case, you should be find a way to trigger defender to create a vss shadow copy.
Opsec
Since the exploit depends on triggering defender,there will obviously be atleast one alert for the malicious file.But there are other IOA’s,the most obvious ones are the strings but the one you want to avoid is the TieringEngineService.exe.As mentioned above, the exploit abuses the TOCTOU to achieve write primitive.So wink wink you should be able to write a hijackable/sideloadable dll into one of the privileged directories . A few ideas I suggest are Win SxS/SysWoW/System32.